
How to Anticipate and Neutralize Digital Breaches with Microsoft Purview and Defender for Cloud Apps
On May 15, 2024, the world witnessed the biggest digital looting of the year. 165 global companies, including AT&T, Ticketmaster, Santander and Neiman Marcus, lost 50 billion sensitive records in weeks. The attackers weren't film experts; they only took advantage of stolen credentials to enter unimpeded. Card numbers, SSN, medical data, employee passwords: everything was exposed.
The real tragedy was not what happened, but what could have been prevented. The lack of a comprehensive protection strategy left the digital doors of these companies open.
The 5 Layers of Armor That Make the Difference
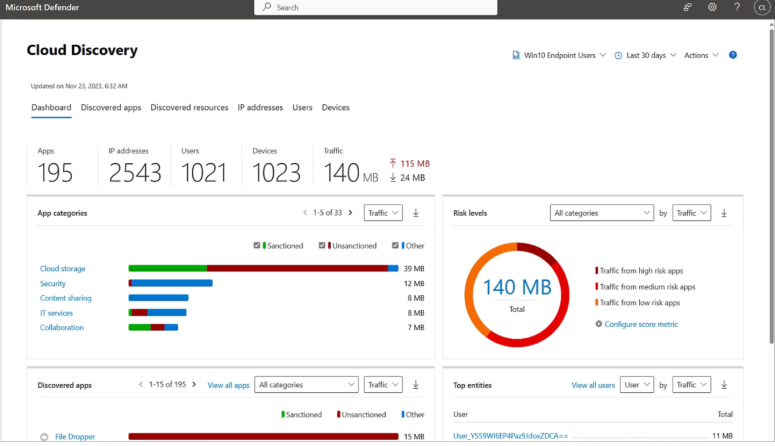
1. Absolute Visibility: Eliminate Shadow IT
The least spoken secret in cloud security: Many companies are unaware that their employees are using unauthorized platforms. Shadow IT is the blind spot where data is left vulnerable. 65% of companies with shadow IT experience data loss without even realizing it.
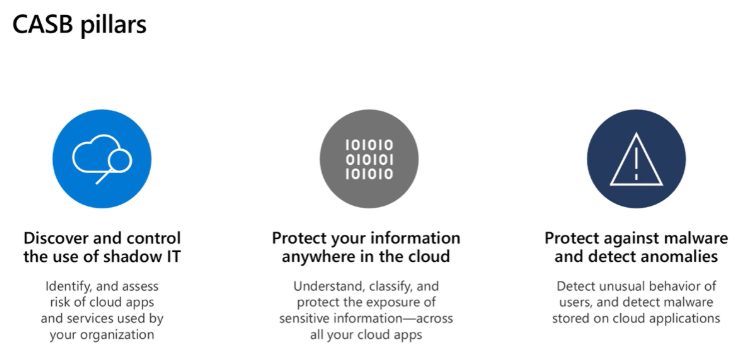
With Defender for Cloud Apps Cloud Discovery, you can catalog more than 31,000 applications in minutes and accurately assess their risk. It detects platforms like Snowflake quickly and blocks unauthorized access in real time, turning chaos into control.
2. Intelligent Anomalous Behavior Detection
The attacker downloaded terabytes in days, an activity that no legitimate user performs. Without monitoring systems, these actions go unnoticed.
With Defender for Cloud Apps Anomaly Detection, machine learning and UEBA profile normal behavior and alert to irregularities such as mass downloads or impossible trips. Thus, breaches are contained in minutes and not in weeks.
3. Real-Time Blocking: Full Session Control
Microsoft's “Session Policies” make it possible to close the digital door just as the attacker tries to extract classified data. It blocks downloads from suspicious IPs, limits access and protects each cloud application as if it were a 24/7 safe.
4. Classification and Advanced Data Protection
Purview Data Map automatically identifies sensitive information such as credit cards, SSN, corporate secrets and labels them according to their level of confidentiality. Purview DLP can prevent top-secret data from being exported, regardless of the user's level of access. The protection is intelligent, adjusted to the critical nature of the content.
5. Shielded Endpoints: Physical Information Control
Is the attacker trying to copy data to a USB, Dropbox, or personal email? DLP endpoints blocks it on the spot. Each laptop becomes a digital vault that is impossible to violate, eliminating the risk of leakage after discharge.
The Inconvenient Truth of Modern Security
It is not enough to control “who enters”. It is essential to know “what they do once inside”. Without granular session controls, data classification, or endpoint protection, attackers find a free field.
Activating all five layers of shielding with Microsoft Purview and Defender for Cloud Apps makes any company an unattractive target for cybercriminals.
Neodefender: Your Strategic Partner in Comprehensive Security
At Neodefender, we don't sell tools; we design custom security architectures. We help you to:
- Get full visibility: Detect shadow IT, shadow AI, and unauthorized apps in your cloud environment.
- Detect anomalies before they become breaches: Machine learning, real-time alerts and UEBA.
- Block data exfiltration instantly: Session control, DLP and advanced classification.
- Protect physical endpoints: Avoid leaks via USB, external applications or email.
There's no such thing as perfect security, but with our architecture, attackers will seek easier targets. The average cost of a breach exceeds $4.44M globally and $10.22M in the U.S. Whereas a successful implementation of Purview and Defender for Cloud Apps costs a fraction and gives you total peace of mind.
Ready to Protect Your Business in 2026?
Request a free 90-minute consultation with Neodefender: we evaluate your current posture, identify critical gaps and design a customized security roadmap.
The next big divide is happening now. The decision is yours: will you be just another victim or a success story in data protection?
Neodefender and Microsoft: We turn security into your greatest competitive advantage.
¡Gracias!
Contacto NeoDefender
.avif)


%20(1).png)

.avif)