
The Future of Enterprise Authentication

The reliance on long, complex passwords, combined with the common practice of reusing them across multiple services, exposes companies to critical risks, ranging from phishing attacks to large-scale credential theft. Today, the business world is moving toward a password-free era. Thanks to the adoption of passkeys within the Microsoft ecosystem, companies have the opportunity to minimize the risks of cyberattacks and transform the way their employees access corporate resources.
Passwords have been the Achilles’ heel of cybersecurity for decades. Companies face daily phishing attacks that compromise credentials, with Microsoft reporting more than 7,000 blocks per second by 2025. This results not only in costly data breaches but also in an operational burden: employees waste time resetting passwords, and IT teams deal with endless support tickets.
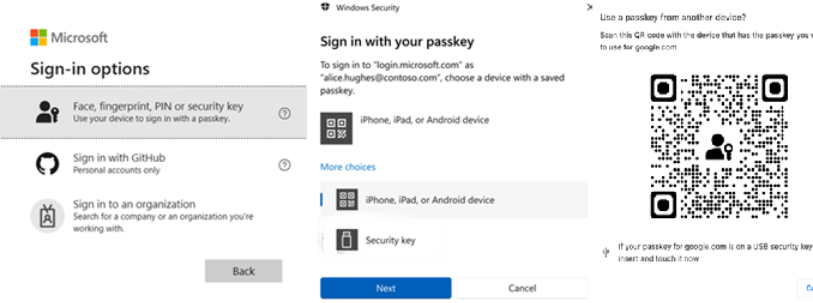
What Are Passkeys?
Passkeys are unique cryptographic credentials stored on the user’s device and authenticated using biometrics such as fingerprint or facial recognition, without transmitting sensitive data to servers. Unlike passwords, passkeys are resistant to phishing because they cannot be reused or intercepted; each one is unique to a specific account and device. Microsoft is making them the default for new accounts starting in 2025, with a cloud-synchronization process that ensures multi-device access without compromising security.
Key Benefits for Businesses
Adopting passkeys with Microsoft offers tangible benefits that go beyond basic security.
- Improved user experience: Logins are up to eight times faster, with a 98% success rate.
- Compliance and scalability: They facilitate compliance with regulations such as GDPR and NIST by eliminating common attack vectors, and scale easily in hybrid environments with Entra ID to support thousands of users.
- Enhanced privacy: Biometric data is processed locally on the device and is never shared, protecting sensitive data in a world of BYOD and remote work.
The Phishing Attack That Nearly Brought Down a Fintech Company
In March 2025, an employee at FinNova Tech receives a phishing email disguised as an “Azure security update”—a spear-phishing attack that referenced company details obtained from LinkedIn. The email includes a link to a fake site that mimics the Microsoft portal, requesting credentials to “verify the account.” Under pressure, the employee enters their username and password, triggering an infostealer (malware that steals credentials from browsers and apps).
Instantly, the attackers gained access to the employee's Entra ID account, which had administrative privileges.
The Solution: Combining Microsoft Services to Prevent Credential-Based Attacks
To mitigate the risks of phishing, credential theft, and infostealers in enterprise environments, we recommend a Zero Trust approach that integrates multiple Microsoft services. This multi-layered strategy prevents initial theft, detects anomalies in real time, and strengthens human resilience.
- Passkeys as the foundation for robust authentication.
- Conditional access for contextual control.
- Detection of risky users.
- Privileged identity management (PIM).
- Anti-phishing training using Microsoft tools (attack simulation).
- Holistic integration and continuous monitoring
This combination of services creates a layered defense: passkeys prevent initial theft, Conditional Access and risky users detect and mitigate it, and training prevents recurrence.
Conclusion
Don’t wait for a security breach to dictate the course of your business. Adopting passkeys not only transforms enterprise authentication but also establishes a new line of defense for your data and reputation. In an environment where protection is key to competing and growing, Microsoft offers a robust ecosystem that enables organizations to anticipate risks and move toward a password-free future, where security is an integral part of business strategy.
Ready to get rid of passwords in just one week?
Contact us today to find out how we can help you implement passkeys in your cloud environment quickly, securely, and seamlessly. Request your personalized consultation now and transform your corporate access strategy.
Recientes
Contacto NeoDefender
.avif)

.png)

%20(2)%20(1)%20(1.png)
.avif)